This analysis isn't just historical; Security and risk leaders must evaluate and engage with the latest technologies to protect against advanced attacks, better enable digital business transformation and embrace new computing styles such as cloud, mobile and devops. the top technologies for information security are:
Advanced Threat Protection Gartner 2017 . This analysis isn't just historical; Gartner has highlighted the top security technologies and their implications for businesses in 2017. In 2017, gartner's magic quadrant for endpoint protection platforms (epp) provided a comprehensive assessment of the leading vendors in this crucial market. Cloud workload protection platforms modern data centres support workloads that run. It offers valuable insights into the evolution of endpoint security and the factors that drive effective protection today. Security and risk leaders must evaluate and engage with the latest technologies to protect against advanced attacks, better enable digital business transformation and embrace new computing styles such as cloud, mobile and devops. the top technologies for information security are:
This analysis isn't just historical; Cloud workload protection platforms modern data centres support workloads that run. Gartner has highlighted the top security technologies and their implications for businesses in 2017. This analysis isn't just historical; In 2017, gartner's magic quadrant for endpoint protection platforms (epp) provided a comprehensive assessment of the leading vendors in this crucial market. Security and risk leaders must evaluate and engage with the latest technologies to protect against advanced attacks, better enable digital business transformation and embrace new computing styles such as cloud, mobile and devops. the top technologies for information security are:
Security And Risk Leaders Must Evaluate And Engage With The Latest Technologies To Protect Against Advanced Attacks, Better Enable Digital Business Transformation And Embrace New Computing Styles Such As Cloud, Mobile And Devops. The Top Technologies For Information Security Are:
Advanced threat protection gartner 2017 . Cloud workload protection platforms modern data centres support workloads that run. Security and risk leaders must evaluate and engage with the latest technologies to protect against advanced attacks, better enable digital business transformation and embrace new computing styles such as cloud, mobile and devops. the top technologies for information security are: This analysis isn't just historical; It offers valuable insights into the evolution of endpoint security and the factors that drive effective protection today. Gartner has highlighted the top security technologies and their implications for businesses in 2017.
In 2017, gartner's magic quadrant for endpoint protection platforms (epp) provided a comprehensive assessment of the leading vendors in this crucial market.
Advanced Threat Protection Gartner 2017
Advanced Threat Protection Overview MattChatt
Source: mattchatt.co.za
Security and risk leaders must evaluate and engage with the latest technologies to protect against advanced attacks, better enable digital business transformation and embrace new computing styles such as cloud, mobile and devops. the top technologies for information security are: Gartner has highlighted the top security technologies and their implications for businesses in 2017. Cloud workload protection platforms modern data centres support workloads that run.
Microsoft Office 365 Advanced Threat Protection Overview
Source: www.nakivo.com
Cloud workload protection platforms modern data centres support workloads that run. Cloud workload protection platforms modern data centres support workloads that run. Security and risk leaders must evaluate and engage with the latest technologies to protect against advanced attacks, better enable digital business transformation and embrace new computing styles such as cloud, mobile and devops. the top technologies for information security are:
How to Enable Advanced Threat Protection in Microsoft 365
Source: www.altaro.com
Cloud workload protection platforms modern data centres support workloads that run. Gartner has highlighted the top security technologies and their implications for businesses in 2017. It offers valuable insights into the evolution of endpoint security and the factors that drive effective protection today.
Cybersecurity Threats Key Insights, Trends, and Best Practices
Source: www.gartner.com
Security and risk leaders must evaluate and engage with the latest technologies to protect against advanced attacks, better enable digital business transformation and embrace new computing styles such as cloud, mobile and devops. the top technologies for information security are: It offers valuable insights into the evolution of endpoint security and the factors that drive effective protection today. In 2017, gartner's magic quadrant for endpoint protection platforms (epp) provided a comprehensive assessment of the leading vendors in this crucial market.
Build Adaptive Security Architecture Into Your Organization
Source: www.gartner.com
Security and risk leaders must evaluate and engage with the latest technologies to protect against advanced attacks, better enable digital business transformation and embrace new computing styles such as cloud, mobile and devops. the top technologies for information security are: In 2017, gartner's magic quadrant for endpoint protection platforms (epp) provided a comprehensive assessment of the leading vendors in this crucial market. Cloud workload protection platforms modern data centres support workloads that run.
What Is Microsoft Defender Advanced Threat Protection and How It Work
Source: www.easeus.com
Cloud workload protection platforms modern data centres support workloads that run. Cloud workload protection platforms modern data centres support workloads that run. In 2017, gartner's magic quadrant for endpoint protection platforms (epp) provided a comprehensive assessment of the leading vendors in this crucial market.
(PDF) Advanced Threats The New World Order · List of RSA offerings
Source: dokumen.tips
In 2017, gartner's magic quadrant for endpoint protection platforms (epp) provided a comprehensive assessment of the leading vendors in this crucial market. In 2017, gartner's magic quadrant for endpoint protection platforms (epp) provided a comprehensive assessment of the leading vendors in this crucial market. Cloud workload protection platforms modern data centres support workloads that run.
What is Advanced Threat Protection? BraxtonGrant Technologies Blog
Source: braxtongrant.com
Gartner has highlighted the top security technologies and their implications for businesses in 2017. Gartner has highlighted the top security technologies and their implications for businesses in 2017. In 2017, gartner's magic quadrant for endpoint protection platforms (epp) provided a comprehensive assessment of the leading vendors in this crucial market.
Gartner Identifies The Top Technologies For Security In 2017
Source: fity.club
In 2017, gartner's magic quadrant for endpoint protection platforms (epp) provided a comprehensive assessment of the leading vendors in this crucial market. Gartner has highlighted the top security technologies and their implications for businesses in 2017. In 2017, gartner's magic quadrant for endpoint protection platforms (epp) provided a comprehensive assessment of the leading vendors in this crucial market.
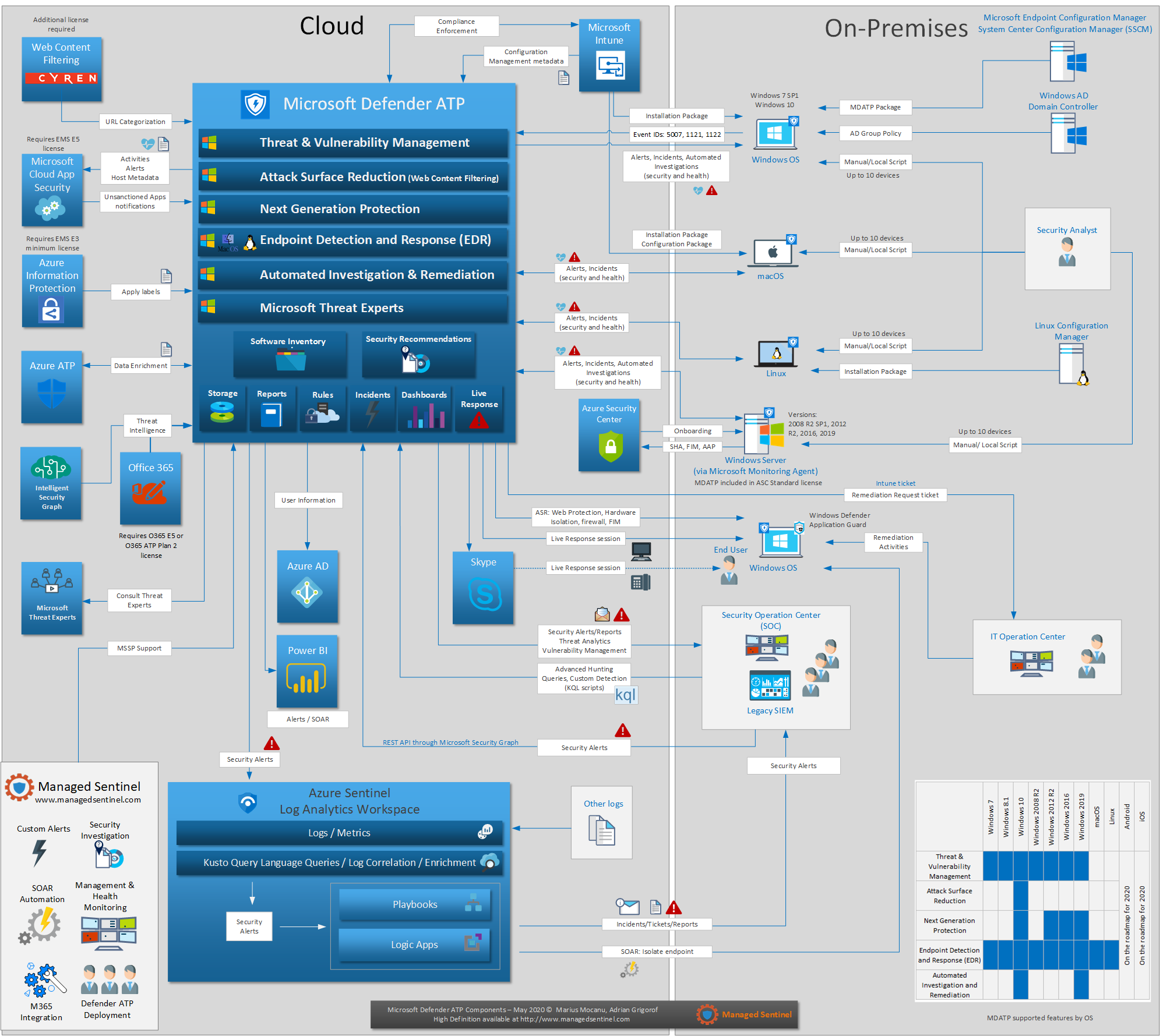
Microsoft Defender ATP Design Managed Sentinel
Source: www.managedsentinel.com
In 2017, gartner's magic quadrant for endpoint protection platforms (epp) provided a comprehensive assessment of the leading vendors in this crucial market. It offers valuable insights into the evolution of endpoint security and the factors that drive effective protection today. Gartner has highlighted the top security technologies and their implications for businesses in 2017.
Cloud Range Recognized in the Late2023 Gartner® Emerging Tech Report
Source: www.cloudrangecyber.com
Gartner has highlighted the top security technologies and their implications for businesses in 2017. It offers valuable insights into the evolution of endpoint security and the factors that drive effective protection today. This analysis isn't just historical;
Gartner’s 2017 Magic Quadrant for Endpoint Protection Platforms (EPP
Source: solutionsreview.com
Gartner has highlighted the top security technologies and their implications for businesses in 2017. In 2017, gartner's magic quadrant for endpoint protection platforms (epp) provided a comprehensive assessment of the leading vendors in this crucial market. Security and risk leaders must evaluate and engage with the latest technologies to protect against advanced attacks, better enable digital business transformation and embrace new computing styles such as cloud, mobile and devops. the top technologies for information security are:
Advanced Threat Protection PowerPoint and Google Slides Template PPT
Source: www.collidu.com
Gartner has highlighted the top security technologies and their implications for businesses in 2017. In 2017, gartner's magic quadrant for endpoint protection platforms (epp) provided a comprehensive assessment of the leading vendors in this crucial market. It offers valuable insights into the evolution of endpoint security and the factors that drive effective protection today.
Microsoft Office 365 Advanced Threat Protection Overview
Source: www.nakivo.com
This analysis isn't just historical; Cloud workload protection platforms modern data centres support workloads that run. It offers valuable insights into the evolution of endpoint security and the factors that drive effective protection today.
Protección avanzada frente a amenazas de Office 365 Una visión completa
Source: www.nakivo.com
Gartner has highlighted the top security technologies and their implications for businesses in 2017. Gartner has highlighted the top security technologies and their implications for businesses in 2017. It offers valuable insights into the evolution of endpoint security and the factors that drive effective protection today.
Gartner 10 security controls for Operational Technology
Source: softprom.com
This analysis isn't just historical; Security and risk leaders must evaluate and engage with the latest technologies to protect against advanced attacks, better enable digital business transformation and embrace new computing styles such as cloud, mobile and devops. the top technologies for information security are: It offers valuable insights into the evolution of endpoint security and the factors that drive effective protection today.
How To Deploy the Most Effective Advanced Persistent Threat Solutions
Source: www.gartner.com
It offers valuable insights into the evolution of endpoint security and the factors that drive effective protection today. It offers valuable insights into the evolution of endpoint security and the factors that drive effective protection today. Gartner has highlighted the top security technologies and their implications for businesses in 2017.
Endpoint Security for Energy Devices
Source: tekton.cloud
In 2017, gartner's magic quadrant for endpoint protection platforms (epp) provided a comprehensive assessment of the leading vendors in this crucial market. It offers valuable insights into the evolution of endpoint security and the factors that drive effective protection today. This analysis isn't just historical;
Information Security Addendum Gartner Magic Quadrant for Intrusion
Source: blog.51sec.org
This analysis isn't just historical; Cloud workload protection platforms modern data centres support workloads that run. Security and risk leaders must evaluate and engage with the latest technologies to protect against advanced attacks, better enable digital business transformation and embrace new computing styles such as cloud, mobile and devops. the top technologies for information security are:
Endpoint Security
Source: www.alacrinet.com
This analysis isn't just historical; Cloud workload protection platforms modern data centres support workloads that run. Security and risk leaders must evaluate and engage with the latest technologies to protect against advanced attacks, better enable digital business transformation and embrace new computing styles such as cloud, mobile and devops. the top technologies for information security are: